Up to $100 billion. That’s how much ad fraud stands to cost the industry in 2023:
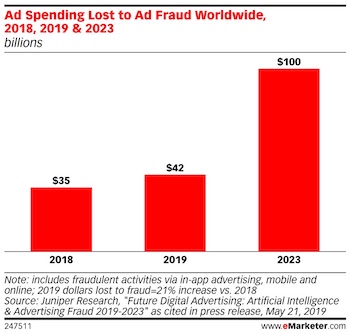
And though it’s prevalent enough that nearly 70% executives call it the biggest hindrance to budget growth, how brands are being stolen from remains a mystery to many. And if you don’t know how you’re being deceived, you stand powerless to prevent it. Today, we cover some of the most common types of ad fraud and how to avoid them.
8 Common types of ad fraud and how to avoid them
As creative as advertisers can be in campaign design and execution, so can fraudsters in their schemes to defraud brands. From domain spoofing to click farms, here are the most common ad fraud schemes, followed by tips on how to avoid them.
1. Domain spoofing
Bidding for ad space takes into account a placement type, website content, traffic quality, etc. The higher placement is in quality, the more a publisher can charge for it. Domain spoofing takes advantage of this system a few different ways, by tricking the advertiser into thinking they’re paying for better inventory than they are:
- URL substitution, the simplest and laziest form of domain spoofing, involves replacing the URL of an actual placement with a fake one. Advertisers think they’re placing an ad one place when they’re bidding for space somewhere else.
- Cross-domain embedding involves the use of two websites: one with high traffic and low-quality inventory, and another with low traffic and quality inventory. Here, the fraudster uses an iframe to overlay the better quality site on the low-quality one with high traffic. This way, websites with brand unsafe content — pornography, hate speech, fake news, etc. — can monetize their traffic by showing their visitors ads from a brand-safe environment. Of course, this is misleading to the advertiser and irrelevant to the visitor.
- Custom browsers can be used by bots to visit any site on the internet, and these bots can make the URL of any site appear to be the URL of a premium site. This URL is reported back to the advertiser, who sees their ad delivered on a site that it was not placed on.
- Human browsers work like traditional malware. When a visitor’s system is infected, and they visit a website, the malware will hijack an ad placement and inject its own.
In all cases, domain spoofing games the system to defraud advertisers and publishers. Simple domain spoofing, like URL substitution, can be caught by diligent advertisers. More complex forms require more complex defenses.
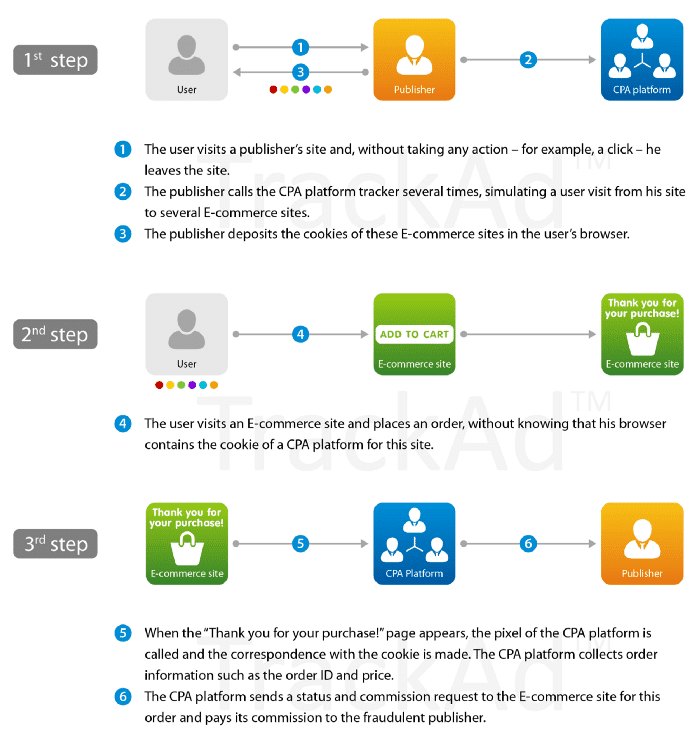
2. Cookie stuffing
Cookies are text files that store information about a visitor’s browsing behavior. They help brands deliver advertising by passing along information relevant to their bid, analytics, creative, etc.
But these cookies can be hijacked and filled with incorrect information about the visitor. It’s common in affiliate marketing, where marketers partner with a brand to advertise their product.
By stuffing text files with false information, the marketer can steal credit for a click, conversion, sale, etc. And by doing so, they get a payout they don’t deserve:
3. Click injection
Click injection is a common form of mobile ad fraud. Like the name makes it sound, click injection is about “injecting” fake clicks into an advertising scenario. These clicks go to an ad or app download, and they result in misattribution, which gives the fraudster credit for producing a click.
Fraudsters employ this scheme through malicious apps that users unknowingly download. Seemingly harmless applications, which might provide wallpaper or a voice changer, for example, will infect a user’s device once downloaded.
There, these apps will run in the background to, as Tech Crunch puts it, click “invisible ads without the user’s knowledge.” By inflating the number of clicks produced, the fraudster can maximize revenue earned from generating the click.
In addition to inflating ad clicks, this scheme can hijack credit for downloads. It’s particularly common on Android devices, which will “broadcast” to all existing apps when a new app is installed on the device. When the malicious app receives this broadcast, it produces a fake click that steals credit for the download and the reward:
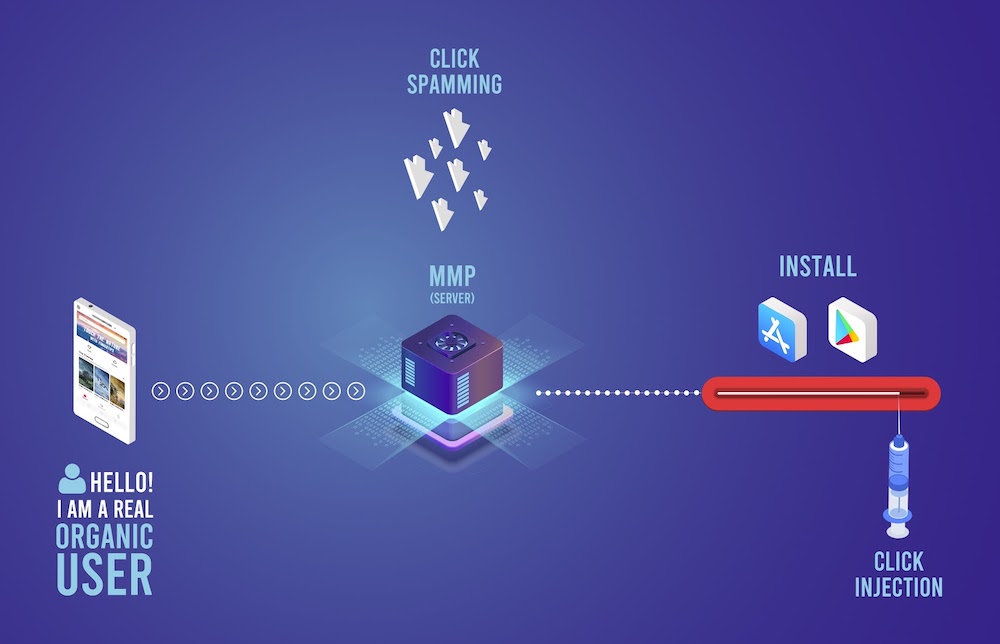
4. Click spamming
Like click injection, click spamming produces dishonest clicks. But instead of faking the click at the last second by injecting rogue code, click spamming will flood a measurement system with low-quality clicks and hope that one of them sneaks through to steal credit. In a blog post for Interceptd, Brittany Irhig offers a helpful analogy:
Click spamming is akin to turning up at the front door of a random stranger and pretending you’re their long-lost relative, hoping they will believe you and invite you in for a free meal. It is unlikely you will be successfully mistaken (misattributed) for the genuine relative; however, if you visit 40 houses every day for a month, you increase your chances of a free feed. Dodgy? Yes. Sophisticated? No. That’s click spamming.
Fraudsters can do this with the help of software, or for clicks that appear more legitimate, even use human-powered click farms. These involve diligent work from groups of low-paid employees whose responsibility is to click on ads or install and uninstall ads to generate revenue. Click farms are often located in other countries, which makes their clicks relatively easy to identify. An influx of clicks from a source like India, for example, is likely evident of a click farm scheme.
5. Pixel stuffing
Imagine how many ads you could show if they were displayed in a 1×1 pixel area! This is what pixel stuffing is.
When fraudsters use pixel stuffing, they’re presenting a larger ad in a space so small it’s undetectable. And even though visitors don’t see it, the fraudsters get credit for the impression. What’s worse, this method can be repeated countless times on a single page:
![]()
6. Ad stacking
Pixel stuffing isn’t the only way to cram more ads than there’s room for on a publisher’s website. When fraudsters want to turn one ad placement into multiple, they can use ad stacking.
To conceptualize ad stacking, imagine you’re at a bookstore walking through aisles and viewing books. You see the cover, but you obviously cannot see the pages. This is similar to what happens to visitors when they arrive on a site where ads are being stacked.
A visitor can see one ad, but it will be “stacked” on top of others, like this:
Here, the visitor only actually sees one ad in one placement, but the fraudster gets credit for showing eight.
7. Ad injection
Injecting clicks is about producing clicks where there are none. Injecting ads can be the same.
Through browser extensions and adware plugins, ad injection allows fraudsters to put ads where they don’t belong.
They can hijack a server to slip an ad of their choosing into a space that belongs to a different advertisement. And according to AdCumulus, they can even place ads on a website that doesn’t normally show ads at all.
8. Geo masking
Where is your traffic coming from? The US? Outside it? Depending on its location, the cost of generating it can change.
Effective targeting of this traffic is central to any campaign. And likely included in that targeting is specific location parameters. If you know your customers tend to generate more value if they’re from the US, you may focus specifically on US customers. When you place the order for your campaign, you’ll be able to specify.
Fraudsters, however, can take your money for high-quality traffic, then sell you traffic that isn’t as valuable. And with a technique called geo masking, they can make that low-quality traffic appear to be high-quality.
The result: They make money on the advertiser paying for low-quality traffic, which appears to be from a high-quality source. Luckily, an advertiser paying close attention to their campaign will notice that numbers won’t add up. They may have a significant number of clicks, but high-value conversions will be very rare.
How to avoid common types of ad fraud
There’s no universal advice for avoiding ad fraud. In some cases, it can be prevented with advertiser diligence. In others, no amount of sleuthing will uncover sophisticated swindling. In a white paper on ad fraud, Ad Form offers some great tips for avoiding ad fraud based on type.
- Fake data: When fraudsters employ hacks that result in inflated data for advertisers, it’s diligence that can stop bleeding ad spend. To ensure a budget isn’t wasted, advertisers will need first to be aware of ad fraud and the ways it can plague campaigns. Secondly, research on a network, open or private, should be done before any major investment. Third, knowledge of brand KPIs and benchmarks can help an advertiser detect when something is fishy. These together can form the mindset needed for catching fake data in reports before too much budget is wasted.
- Fake supply: In the cases of domain spoofing and ad injection, the solution is the adoption of industry standards. With the introduction of ads.txt — a list file of authorized ad vendors which publishers can add to their site — the IAB has attempted to curb domain spoofing. A majority 80% of programmatic video ad publishers have adopted it since.
More recently, app-ads.txt was developed to lower fraud on mobile, and ad.cert now aims to prevent ad injection. Adopting these standards will bring a level of transparency that will make it more difficult for fraudsters to infiltrate publishers.
- Fake traffic: Bots, ad stacking, click farms, pixel stuffing — these forms of manipulating traffic are among the most prevalent forms of ad fraud. The solution is the advancing technology built to combat such techniques, which can detect and react to ad fraud at different stages of the transaction process. Says Ad Form: It can be used during the pre-bid phase to identify suspicious domains, IP addresses of the User or even Cookie ID and refuse to bid in those auctions. Or, if the technology does not detect a threat until after the ad has been served, it can report and not register the fake impression, logging the fraud to be avoided in future bids.
Drive real clicks and convert more with Instapage
A good portion of ad fraud can be prevented through advertiser diligence. With Instapage, you’ll not only be able to create personalized landing pages that turn real clicks into conversions, but you’ll also have the industry’s most advanced analytics dashboard to monitor KPIs and take ownership of your data.
Sign up for an Instapage 14-day free trial today.
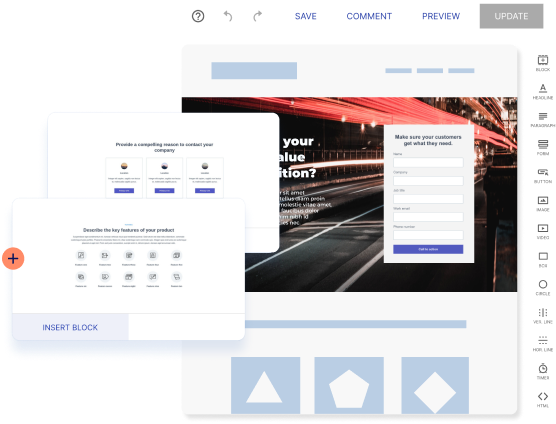
Try the world's most advanced landing page platform with a risk-free trial.
